Network traffic anomaly classification |
Our goal is to provide a detailed classification of anomalies in the MAWILab repository.
We use a detailed, tree-based taxonomy. The taxonomy is completely defined by a set of files. A single file define the taxonomy tree while several other files define each node of the tree.
The classification tool process network traffic and use the previously defined taxonomy to classify events.
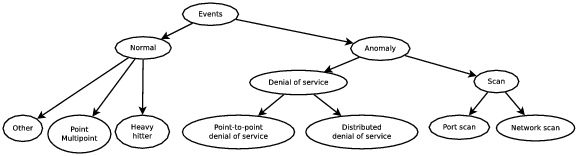
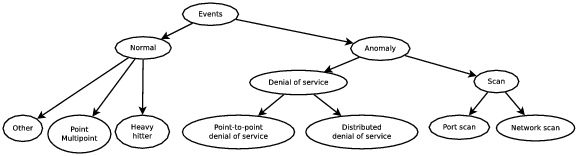
The taxonomy structure is defined as a tree. Each node of the tree is labeled. Some of them are associated with a signature. The picture below is a high-level description of the tree structure.
Below is a example of signature for a UDP network scan. We characterize a UDP network scan as a set of packets with a small number of sources, a high number of destinations, a small number of packets for each destination (which is consistent with probing activity), and a high proportion of UDP packets.
Using our taxonomy, this can be expressed with the following signature:
nb_src_addr < 5
∧ nb_dst_addr >= 20
∧ nb_packets/nb_dst_addr < 5
∧ nb_udp_packets/nb_packets >= 0.8
Several versions of the taxonomy are available: v1.23 (Trac2014 version) / v1.33 (MAWILab 1.1 version) / v1.43 (The latest version) .
This tool’s source code is not yet available but a binary executable is available upon request.
This work is further explained in detail in this paper [1].
Here is the bibtex:
@inproceedings{Mazel2014TRAC,
author = {Mazel, Johan and Fontugne, Romain and Fukuda, Kensuke},
title = {A Taxonomy of Anomalies in Backbone Network Traffic},
booktitle = {Proceedings of 5th International Workshop on
TRaffic Analysis and Characterization},
pages={30-36},
year = {2014},
series = {TRAC 2014}
}
This document was translated from LATEX by HEVEA.